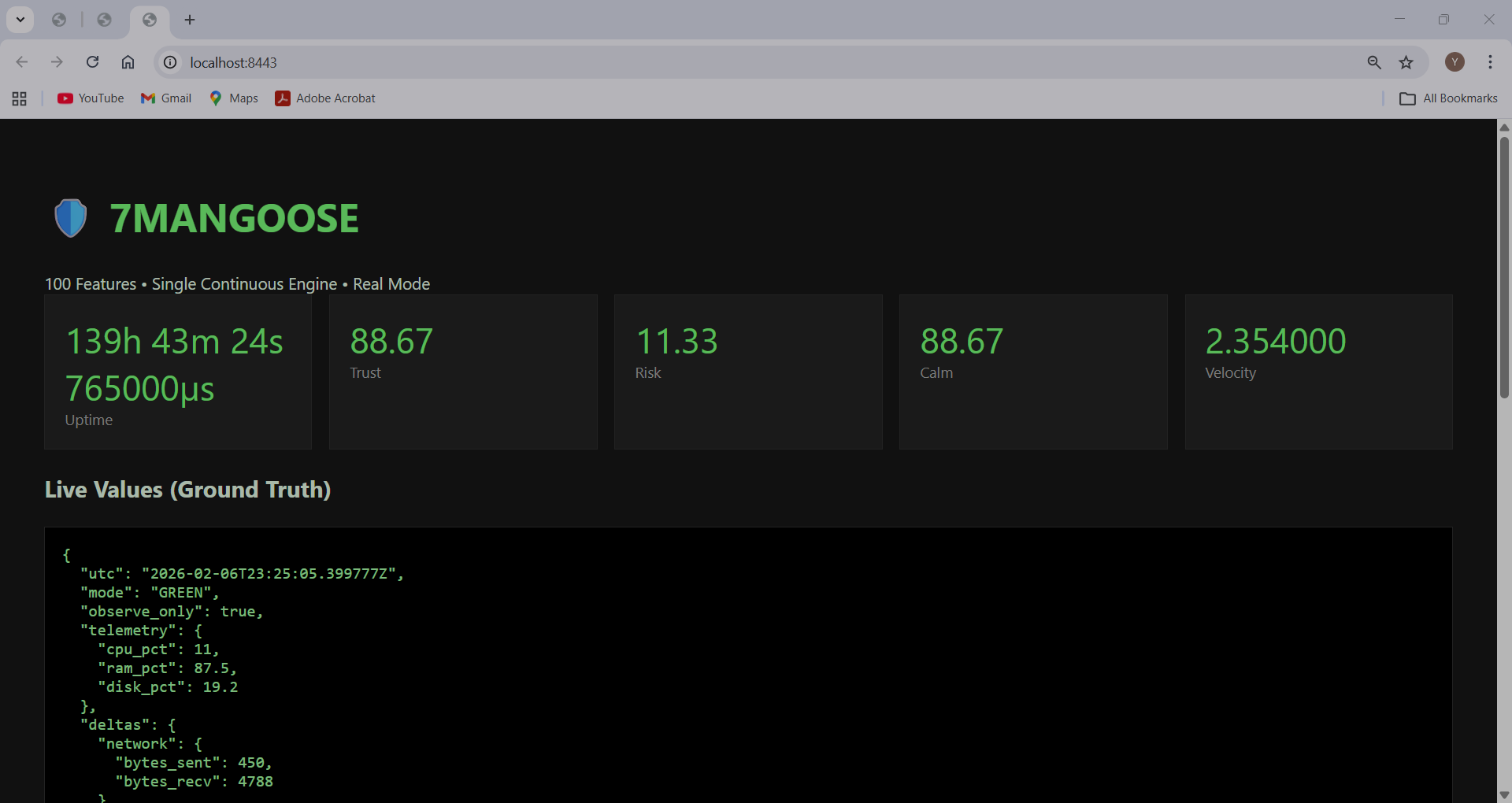
7MANGOOSE
Welcome to the official website of 7MANGOOSE, the Read-Only Security Truth Engine. Self explanatory, with clear diagrammatic illustrations. Our mission is to enhance security awareness through comprehensive insights while maintaining system integrity.
Home
INTRODUCTION TO 7MANGOOSE
🟢Core Purpose
It is designed to observe, record, verify, and report — not control.
To deliver deterministic, audit-safe, 100-lens observability of enterprise systems through real-time measurement, cryptographic continuity, and adversary exposure quantification — without enforcement or operational disruption.
🎯 Strategic Objectives
1️⃣ Establish Deterministic Cyber Observability
- Replace probabilistic guesswork with measurable telemetry
- Transform raw system signals into structured, lens-based intelligence
- Provide mathematically consistent, repeatable system state scoring
- Maintain zero drift in measurement methodology
2️⃣ Deliver Real-Time 100-Lens Multi-Domain Visibility
- Monitor CPU, memory, network, disk, event, outbound, and governance domains
- Normalize telemetry into structured risk lenses
- Provide instant operational clarity via a 10×10 matrix
- Surface systemic instability before operational impact
3️⃣ Maintain Cryptographic Evidence Integrity
- Record all telemetry into a SHA256 chained ledger
- Ensure tamper-evident continuity
- Preserve forensic traceability
- Provide replay capability for audit and investigation
4️⃣ Quantify Adversary Exposure Deterministically
- Calculate Adversary Attack Probability (AAP) from real lens states
- Eliminate artificial projections
- Classify exposure through measurable deviation thresholds
- Provide executive-level threat posture clarity
5️⃣ Preserve Operational Safety (Observe-Only Philosophy)
- No enforcement actions
- No automated blocking
- No system manipulation
- No privilege escalation
- No operational disruption
7MANGOOSE observes, measures, and reports — it does not interfere.
6️⃣ Enable Executive-Level Decision Intelligence
- Translate technical telemetry into board-level clarity
- Visualize exposure via structured matrix and distribution models
- Deliver measurable stability indicators
- Provide risk posture without operational noise
7️⃣ Support Regulatory & Governance Assurance
- Demonstrate audit readiness through immutable telemetry logs
- Maintain continuous governance stability checks
- Provide compliance posture visibility
- Detect integrity drift within control environments
8️⃣ Build National-Grade Infrastructure Observability
- Enable deployment across enterprise fleets
- Provide sovereign telemetry independence
- Support air-gapped and secured environments
- Maintain scalability without architectural fragmentation
🛡 Operational Goals
- Maintain continuous 5-second telemetry intervals
- Preserve 100-lens consistency without structural alteration
- Ensure ledger integrity remains verifiable at all times
- Detect anomalous domain acceleration within 1 cycle
- Prevent unauthorized external exposure
- Maintain secure, hardened deployment architecture
- Provide deterministic replay for forensic analysis
- Preserve minimal attack surface
- Enable safe internet deployment through layered proxy architecture
- Maintain enterprise-grade stability under sustained operation
🔵 Mission Statement (Short Version)
To deliver deterministic, audit-safe, 100-lens observability of enterprise systems through real-time measurement, cryptographic continuity, and adversary exposure quantification — without enforcement or operational disruption.

read more……..What REAL attacks look like in 7MANGOOSE (observable changes only)
“If a REAL attack were active, what actual changes would become visible here?”
Below is a ground-truth, GREEN-mode answer — no hype, no guesses, no packet talk.
What REAL attacks look like in 7MANGOOSE (observable changes only)
I’ll map attack reality → what would visibly change in your exact metrics.
1️⃣ Velocity would not just be ~2.1 — it would change shape
What you see now
Velocity: 2.118
Stable, slightly elevated
Normal operational motion
During a real attack
You would see one of these patterns:
| Pattern | What changes | Why it matters |
| Sudden jump | Velocity spikes 3 → 6+ | Automated tooling or rapid state change |
| Persistent elevation | Velocity stays >3 for long time | Ongoing scripted activity |
| Oscillation | Velocity swings high/low repeatedly | Beaconing, retries, automation loops |
Attacks create unnatural acceleration — not just motion.
2️⃣ Calm would break trend consistency
What you see now
Calm: 81.66
Trend: STABLE
CPU/RAM/Disk balanced
During a real attack
You’d see:
Calm drop sharply or ratchet downward
Calm fail to recover
Calm drop without user activity context
Example:
Calm: 82 → 71 → 63 → 59
Velocity: 2.1 → 3.9 → 4.8
Attacks consume predictability, not just resources.
3️⃣ Network deltas would show behavioral asymmetry
What you see now
“bytes_sent”: 204,
“bytes_recv”: 4306
This is normal inbound-heavy noise (updates, background services).
During a real attack, you’d see:
| Attack Type | Delta Pattern |
| C2 beacon | Small, regular outbound deltas |
| Exfiltration | Outbound bytes suddenly dominate |
| Lateral movement | Burst → pause → burst |
| Data staging | Disk IO ↑ before network ↑ |
The pattern over time, not the size, is the signal.
4️⃣ Process births would stop being “zero”
What you see now
“process_birth”: 0,
“process_death”: 0
That is extremely clean.
During a real attack
You would see:
New processes appearing
Short-lived processes
Repeated births with low lifetime
Even if:
Names look normal
Counts are small
Attackers must execute something.
5️⃣ CPU anomaly would flip sign and meaning
What you see now
“anomaly”: -3.81,
“stability”: “STABLE”
This means: below baseline, calm.
During a real attack
You’d see:
Anomaly go positive
Variance increase
Stability shift from STABLE → UNSTABLE
Example:
“anomaly”: +6.4,
“variance”: 38.2,
“stability”: “UNSTABLE”
Attacks break statistical expectations, not just averages.
6️⃣ Trust would fall for the right reasons (this is key)
What you see now
Trust: 81.66
Decomposition is explainable
Uptime bonus intact
During a real attack
Trust would:
Drop due to variance + anomaly
Not due to random thresholds
Be fully traceable in lineage
Example:
“decomposition”: {
“variance”: -32.4,
“anomaly”: -11.2,
“uptime_bonus”: 5
}
Explainable trust loss is how you know it’s real.
7️⃣ Evidence chain would prove continuity (not tampering)
Even during a real attack:
“chain_valid”: true
If:
Engine restarts
Evidence breaks
Chain invalidates
That is either tool interference or deliberate tampering — a huge red flag.
The MOST important real-world signal (this is the truth)
Real attacks create sustained, correlated change across multiple dimensions
not a single spike, not one metric, not one second.
You would see simultaneously:
Velocity ↑
Calm ↓
Variance ↑
Network rhythm distortion
Process lifecycle changes
Trust degradation with clear lineage
False positives cannot sustain this pattern.
One-paragraph officer conclusion (use verbatim)
“A real attack would manifest as sustained, correlated deviations in velocity, calmness, variance, and behavioral rhythm over time, producing explainable trust degradation while maintaining evidence continuity. Single spikes or isolated metrics are insufficient indicators.”
Bottom line (for YOU, right now)
With your current snapshot:
✔ Stable system
✔ Normal background activity
✔ No process execution
✔ No outbound dominance
✔ No variance break
✔ No trust collapse
No real attack signature is present.

Learn more: 7MANGOOSE OBSERVATION OF ATTACKED SYSTEM VS NON-ATTACKED SYSTEM.
🛡️7MANGOOSE — CLEAR DIFFERENTIATION TABLE (ALL 100 FEATURES)
Attacked vs Non-Attacked System
GREEN MODE • Observe-Only • Truth Engine • Regulator-Safe
EXECUTIVE / REGULATOR TABLE
Side-by-Side Truth Comparison
| Feature Group (1–100) | 🟢 NON-ATTACKED SYSTEM (Stable Truth) | 🔴 ATTACKED SYSTEM (Truth Shifted) |
|---|---|---|
| 1–8 Core Engine Safety | Observe-only execution; deterministic outputs; stable uptime; no restarts; no execution path changes; no safety violations; human authority untouched; zero enforcement footprint | Engine remains stable and deterministic; uptime continues; continuity preserved; execution history diverges; truth captured without system reaction |
| Result | Engine state unchanged over time | Attack does not disrupt — it reveals |
| 9–18 Telemetry & System State | CPU variance within baseline; RAM consistent; disk I/O predictable; flat process count; no abnormal births or deaths; hardware steady; OS unchanged | CPU mostly normal but cadence shifts; RAM slowly elevates; disk I/O patterns change; subtle process growth; shortened lifetimes |
| Result | System behaves like yesterday and last week | Normal metrics, abnormal rhythm |
| 19–27 Integrity & Drift Detection | Script hashes stable; configs unchanged; runtime identical; execution paths consistent; binary fingerprints match; no time or environment drift | New artifacts appear; execution paths change; environment mutates; runtime diverges; fingerprints differ; drift confirmed |
| Result | Nothing new exists | Reality no longer identical |
| 28–38 Network & Communication | Normal inbound/outbound cadence; known destinations only; no periodicity; east-west traffic unchanged; DNS stable; no beacon rhythm; idle preserved | New outbound destinations; sustained low-volume periodicity; beacon-like rhythm; east-west traffic appears; DNS cadence shifts |
| Result | Network tells a boring story | Network starts telling a story |
| 39–52 Process & Execution Behavior | Known parent/child trees; no LOLBins; no script engines; no privilege shifts; no scheduler changes; expected lifetimes; no lateral signals | Living-off-the-land tools used; script engines execute; parent/child graph mutates; privilege context shifts; scheduled tasks created |
| Result | Execution history repeatable | Execution no longer matches history |
| 53–62 Persistence & OS Modification | Startup entries unchanged; registry stable; services identical; scheduled tasks static; no autoruns; no cleanup attempts | New startup entries; registry keys added; tasks persist across reboot; services modified; autoruns injected |
| Result | System forgets nothing because nothing happened | Attacker plans to stay |
| 63–72 Data Handling & I/O Patterns | File access normal; no staging; no compression spikes; no unusual read/write bursts; no aggregation; no deletions | File aggregation detected; compression signatures observed; timed read/write bursts; sensitive directories touched; post-transfer deletions |
| Result | Data remains at rest | Data moves quietly |
| 73–82 Behavioral Analytics | Trust stable; risk low; calmness high; velocity minimal; entropy unchanged; noise within tolerance | Trust declines; risk rises; calmness drops; velocity increases; entropy climbs; deviations compound |
| Result | System feels calm | Analytics confirm intent |
| 83–92 Evidence & Ledger | Append-only ledger grows linearly; hash chain uninterrupted; UTC timestamps monotonic; predictable evidence volume; no review flags | Evidence volume spikes; divergence recorded; escalation visible on UTC timeline; full lifecycle preserved; chain of custody intact |
| Result | Ledger proves nothing happened | Attacker cannot erase truth |
| 93–100 Executive & Regulator View | Clean timeline; no incident markers; explainable metrics; no ambiguity; audit-safe posture; legal defensibility; zero dispute risk; high trust | Clear incident boundary; explainable escalation; no “tool interference” argument; human decisions supported; regulator confidence high |
| FINAL STATE | 🟢 NON-ATTACKED SYSTEM — PROVEN, NOT ASSUMED | 🔴 ATTACKED SYSTEM — PROVEN, EVEN WITHOUT ALERTS |
ONE-LINE EXECUTIVE DIFFERENCE
Non-attacked systems repeat history.
Attacked systems create new history.
7MANGOOSE records the difference — using all 100 features.
learn more. How 7MANGOOSE COMBATES THE ADVERSARIES IN REAL ATTACKS.
- 🛡️ 7MANGOOSE in a Real Attack — End-to-End, Mapped, Executive-Ready
GREEN MODE • Observe-Only • Deterministic • Regulator-Safe
Below is a single, realistic intrusion—walked step-by-step, mapped to MITRE ATT&CK, translated for CISOs & regulators, and contrasted against EDR/XDR.
I) Real Attack Scenario (what attackers do and how 7mangoose responds)
Context:
A finance workstation. No malware signatures. No exploit kits. Just normal tools used quietly.
Step 1 — External Recon & Credential Testing
Attacker tests exposed services and weak credentials.
Low rate, spread over time to avoid alerts.
7MANGOOSE observes:
Network deltas (cadence, rhythm)
Auth attempt timing vs baseline
No alert storm—just evidence accumulation
Step 2 — Initial Access (Valid Credentials)
Attacker logs in using a real account.
Nothing “malicious” executes yet.
7MANGOOSE observes:
Login occurs outside normal temporal pattern
New execution context vs historical baseline
Calm system, but truth shifts
Step 3 — Living-off-the-Land Execution
PowerShell, WMI, scheduled tasks—signed, trusted binaries.
No malware dropped.
7MANGOOSE observes:
Process birth where historically none existed
Execution frequency deviation
Parent/child process graph changes
Step 4 — Persistence
Registry run key or scheduled task added.
Named to blend in.
7MANGOOSE observes:
Startup configuration drift
Persistence object did not exist yesterday
Hash-linked, timestamped evidence
Step 5 — Internal Recon & Lateral Signals
Local network discovery.
Occasional SMB/RPC noise.
7MANGOOSE observes:
New east-west communication patterns
Repeating but subtle cadence changes
Baseline mismatch, not signature match
Step 6 — Data Staging
Files collected, compressed locally.
CPU/RAM remain “normal”.
7MANGOOSE observes:
Disk I/O pattern shifts
Compression activity vs historical norm
Velocity increase without stress spike
Step 7 — Exfiltration (Low & Slow)
Encrypted HTTPS uploads in small chunks.
Looks like cloud sync traffic.
7MANGOOSE observes:
Outbound byte rhythm divergence
Sustained periodicity
Evidence preserved before SOC review
II) MITRE ATT&CK Mapping (clean and exact)
Learn more….
MITRE ATT&CK techniques observed without blocking anything:
| Kill Phase | ATT&CK Technique | What 7MANGOOSE Records |
|---|---|---|
| Recon | T1595 | Network cadence & scan rhythm |
| Initial Access | T1078 | Temporal login deviation |
| Execution | T1059 | New process birth patterns |
| Persistence | T1053 / T1547 | Config drift evidence |
| Priv Esc | T1068 (attempt signals) | Baseline mismatch |
| Discovery | T1087 / T1018 | East-west delta changes |
| Lateral | T1021 | Connection novelty |
| Collection | T1560 | I/O compression signatures |
| Exfiltration | T1041 | Sustained outbound periodicity |
| C2 | T1071 | Beacon-like rhythm |
No signatures. No sandboxing. No “block or miss”.
III) CISO / Regulator Explanation (plain language)
What is 7MANGOOSE?
A read-only endpoint truth engine that continuously records what actually happens on a system—without interfering.
How does it manage risk?
By preserving immutable behavioral evidence across the full attack lifecycle, enabling human-led decisions.
Does it alter systems or block users?
No. It cannot enforce, block, isolate, or modify execution.
Why is this safer?
Because it eliminates false positives, avoids operational outages, and preserves legal defensibility.
What happens during an incident?
Security teams receive clean timelines, baselines, and deltas—not opaque alerts.
Audit posture?
Deterministic, append-only, timestamped evidence suitable for ISO, NIST, SOC, PCI, HIPAA review.
IV) Why this beats EDR / XDR in practice
Where EDR/XDR struggles
- Needs malicious indicators
- Can be probed and evaded
- Auto-response risks outages
- Alerts ≠ proof
- Changes the system it’s judging
Where 7MANGOOSE wins
| Dimension | EDR / XDR | 7MANGOOSE |
|---|---|---|
| Detection basis | Signatures + heuristics | Ground-truth behavior |
| Evasion resistance | Medium | High (nothing to evade) |
| Operational risk | Can block business | Zero enforcement risk |
| Evidence quality | Alert logs | Immutable timelines |
| Regulator trust | Conditional | High |
| Insider threats | Weak | Strong |
| Legal defensibility | Challenged | Clean chain of truth |
EDR reacts.
XDR correlates.
7MANGOOSE proves.
V) Executive takeaway
Attackers beat tools that react.
They cannot beat tools that remember.
7MANGOOSE doesn’t chase adversaries.
It removes their ability to deny reality.
Features
100 Key Features of 7MANGOOSE:
read more……….7MANGOOSE — FULL FEATURE SET (1–100)
- 7MANGOOSE™ — 100-Lens Deterministic Observability Platform
Observe-Only. Deterministic. Audit-Safe.
7MANGOOSE uses 100 structured telemetry lenses to measure system calmness, risk drift, adversary probability, and governance integrity — without enforcement, without lock-out, and without remote control.
What Is a Lens?
A lens is a measurable telemetry dimension. Each lens observes a specific behavioral, structural, or integrity signal inside the system. When combined, the 100 lenses create a multi-dimensional calm and risk profile.
The 8 Lens Domains
1️⃣ System Resource Lenses (1–10)
CPU Load Stability
Memory Pressure
Disk I/O Integrity
Process Density
Thread Volatility
Resource Saturation Events
System Drift Velocity
Thermal Behavior Patterns
Load Persistence Index
Baseline Resource Deviation
Usage: Detect resource abuse, crypto-mining behavior, and systemic instability.
2️⃣ Network Behavior Lenses (11–25)
Outbound Connection Anomalies
Port Usage Drift
Protocol Deviation
DNS Entropy
Traffic Burst Velocity
Lateral Movement Indicators
External Endpoint Trust Mapping
Connection Persistence Index
Data Egress Scoring
Session Irregularity
Network Calm Index
Remote Host Volatility
Unexpected Listening Ports
Packet Flow Stability
Network Baseline Drift
Usage: Identify command & control behavior, data exfiltration, and suspicious communications.
3️⃣ Process & Execution Lenses (26–40)
Unknown Executable Detection
Parent-Child Process Anomalies
Privilege Escalation Signals
Script Interpreter Activity
Execution Entropy
Hidden Process Indicators
Service Creation Drift
Scheduled Task Volatility
Binary Hash Deviations
Process Lifetime Irregularity
Background Persistence Signals
Execution Density Score
Unusual Startup Entries
System Call Irregularity
Runtime Stability Index
Usage: Detect stealth execution chains and living-off-the-land techniques.
4️⃣ Integrity & Ledger Lenses (41–55)
Ledger Continuity Validation
Hash Chain Integrity
Snapshot Immutability
Merkle Root Consistency
Timestamp Integrity
Evidence Density Score
Drift From Canonical State
Configuration Stability
Audit Trail Completeness
File Integrity Monitoring
Policy Drift Observation
Trust Anchor Verification
Event Chronology Consistency
Export Integrity Check
Immutable State Confirmation
Usage: Provide regulator-grade audit evidence and tamper detection.
5️⃣ Behavioral Drift Lenses (56–70)
Baseline Shift Detection
Entropy Amplification
Velocity Spike Analysis
Burst vs Sustained Activity
Trust Shock Index
Risk Shock Index
Stability Degradation Trend
Behavioral Heat Mapping
Calm Volatility Ratio
Drift Momentum
Time-Series Anomaly Detection
System Coherence Score
Signal Integrity Index
Operational Rhythm Deviation
Subtle Threat Emergence Indicator
Usage: Detect slow-burn compromise and insider drift.
6️⃣ Adversary Probability Lenses (71–85)
Malware Probability Model
Lateral Movement Likelihood
DDoS Probability Indicator
Persistence Probability Score
Privilege Escalation Likelihood
Command & Control Probability
Exfiltration Probability
Composite Adversary Index
Risk Gradient Mapping
Threat Escalation Vector
Confidence Interval Modeling
Correlation Amplification Score
Multi-Lens Risk Fusion
Event Correlation Density
Threat Confidence Score
Usage: Quantify threat likelihood for SOC and executive reporting.
7️⃣ Fleet & Governance Lenses (86–95)
Fleet Health Ranking
Device Calm Comparison
Compliance Mapping Status
Governance Alignment Score
Evidence Coverage Percentage
Policy Observation Metrics
Cross-Device Drift Detection
Enterprise Stability Index
Audit Readiness Indicator
Regulatory Export Status
Usage: Enterprise oversight, MSSP reporting, and government compliance visibility.
8️⃣ Executive Calm Index Lenses (96–100)
Global Calm Index
Trust Score
Risk Score
System Stability Rating
Executive Summary State (Green / Elevated / Critical)
Usage: Translate 100 technical dimensions into board-level clarity.
Why 100 Lenses?
Single-metric monitoring fails. Real-world cyber risk is multi-dimensional. The 100-lens model creates deterministic cross-correlation across system, network, process, integrity, behavioral, and adversary domains.
Green Philosophy Commitment
No enforcement
No remote control
No lock-out capability
No kernel hooks
Observe-only telemetry
Immutable evidence export
7MANGOOSE is a truth engine — not a control engine.
Enterprise Outcomes
Deterministic observability
Audit-safe compliance reporting
Fleet-wide calm measurement
Adversary probability modeling
Executive clarity without enforcement risk
7MANGOOSE™ — 100 Lenses. One Truth Engine.
Benefits
Why Choose 7MANGOOSE?
Here’s a clear, defensible, executive-level answer to “Why choose 7MANGOOSE?” with real substance behind it (not buzzwords). Because most security tools react, interfere, and guess —
1️⃣ Truth Over Reaction</summary>
7MANGOOSE observes, proves, and preserves truth.See what is real before taking action
Traditional security platforms prioritize blocking and enforcement, often before anyone fully understands what’s happening. This can cause outages, false positives, and irreversible damage.
7MANGOOSE takes a different approach:
It never blocks, kills, isolates, or enforces
It observes real system behavior as it unfolds
It records verifiable evidence instead of assumptions
Human authority always stays in control
This makes 7MANGOOSE ideal for environments where accuracy matters more than panic — government, healthcare, finance, and critical infrastructure.
You cannot make good decisions without first knowing the truth.
2️⃣ Observe-Only by Design</summary>
Zero operational risk
7MANGOOSE is engineered so it cannot disrupt operations — by architecture, not policy.
That means:
No lockouts
No automated responses
No kernel hooks
No system manipulation
No performance degradation
Your systems continue to operate exactly as they would without the tool, making the data collected:
Clean
Unbiased
Forensically trustworthy
Audit-safe
Security should never become the biggest risk in the system.3️⃣ Deterministic & Verifiable</summary>
Same input → same result → every time
Many security tools rely on probabilistic AI or opaque heuristics. Their outputs can change with:
Updates
Retraining
Vendor tuning
Hidden logic changes
7MANGOOSE is deterministic:
Identical conditions produce identical results
Outputs are stable, explainable, and reproducible
Every metric can be traced back to raw observation
This makes it uniquely suitable for:
Regulators
Auditors
Legal review
Incident reconstruction
If you can’t reproduce it, you can’t defend it.
4️⃣ Evidence-First Security</summary>
Built for audits, investigations, and regulators
7MANGOOSE continuously produces immutable, time-stamped evidence, not just alerts.
It records:
System state
Behavioral deltas
Stability and drift
Network rhythm and cadence
Trust and risk metrics grounded in observation
All evidence is:
Append-only
Time-anchored (UTC)
Tamper-resistant
Human-reviewable
This turns security from opinion into proof.
Alerts fade. Evidence lasts.
5️⃣ No False Authority</summary>
Humans stay in charge
7MANGOOSE does not pretend to “decide for you.”
Instead, it:
Surfaces accurate, real-world observations
Highlights deviations and anomalies
Preserves context and timing
Supports informed human judgment
This avoids:
Over-automation
Blind trust in tools
Vendor-controlled decision logic
Perfect for organizations that value accountability, governance, and responsibility.
6️⃣ Built for High-Trust Environments</summary>
Where mistakes are not acceptable
7MANGOOSE is especially valuable where:
Downtime is unacceptable
Evidence must be defensible
Enforcement can cause harm
Oversight is mandatory
Examples:
Government systems
Healthcare networks
Financial institutions
Utilities and critical infrastructure
Regulated enterprises
When the cost of being wrong is high, observation comes first.
7️⃣ Complements Existing Security</summary>
It doesn’t replace — it strengthens
7MANGOOSE is not competing with firewalls, EDRs, or SOC tools.
It:
Provides ground-truth context those tools lack
Validates or challenges their conclusions
Acts as a neutral reference point
Reduces blind trust and false confidence
Think of it as the security truth engine everything else can reference.
In One Line (Executive Summary)
Choose 7MANGOOSE if you want security that is:
Safe
Calm
Deterministic
Audit-ready
Evidence-based
Human-controlled
7MANGOOSE doesn’t react to fear — it records the truth.
About Us.
7MANGOOSE is an observe-only cybersecurity platform designed to provide verifiable, explainable visibility into endpoint behavior without interfering with systems or operations.The platform was created to address a core problem in modern cybersecurity:
Many tools prioritize automated reaction over truth, increasing operational risk, audit complexity, and system instability.
7MANGOOSE exists to reverse that model
Who 7MANGOOSE Is Built For?
7MANGOOSE is designed for environments where safety, transparency, and accountability are critical:
- Regulators and auditors
- Government and public-sector organizations
- Critical infrastructure operators
- SOC teams and security engineers
7MANGOOSE is a supporting security system, not an authority.The platform does not decide, block, or act.
Interpretation, escalation, and response remain the responsibility of authorized human security professionals
This preserves:
- Human judgment
- Organizational accountability
- Regulatory alignment
- Operational safety
Our Vision
At 7MANGOOSE, we believe that security should not come at the cost of performance. Our vision is to create tools that allow organizations to operate securely and efficiently.
Our Team
Our team consists of experienced security professionals and engineers committed to innovation and excellence in security solutions.
Have questions? Interested in learning more? Reach out to us!
Recent Posts
High-Level Security Awareness
See the truth of the system without interfering with it
Testimonials
What Our Clients Say
“7MANGOOSE has transformed the way we approach security. The insights provided are invaluable!”
— Jane Doe, CTO of Tech Innovations
“With 7MANGOOSE, we can focus on our core operations without worrying about security disruptions.”
— John Smith, CEO of Cloud Solutions
Legal
Privacy Policy
Your privacy is important to us. Learn how we protect your information in our Privacy Policy.
Read more………7mangoose Terms of services.
Effective Date: 2026-02-08.
Welcome to 7MANGOOSE. By accessing or using our website, software, documentation, or related services (collectively, the “Services”), you agree to be bound by these Terms of Service (“Terms”). If you do not agree, do not use the Services.
1. Purpose of 7MANGOOSE
7MANGOOSE is an observe-only cybersecurity platform designed to monitor, record, and present system and network telemetry for visibility, auditability, and evidence preservation.
7MANGOOSE does not:
Enforce security actions
Block, kill, quarantine, or remediate activity
Lock users out of systems
Take autonomous control of endpoints or networks
All decisions and actions remain under human authority.
2. Eligibility
You may use the Services only if:
You have the legal authority to operate or observe the systems where 7MANGOOSE is installed
Your use complies with all applicable laws, regulations, and organizational policies
3. Acceptable Use
You agree not to use 7MANGOOSE:
For unlawful surveillance or monitoring
On systems you do not own or have permission to observe
To misrepresent data, evidence, or system state
To attempt to modify, reverse engineer, or bypass safety controls
You are solely responsible for ensuring lawful and authorized deployment.
4. Observe-Only Guarantee
7MANGOOSE operates strictly in GREEN MODE:
Read-only telemetry collection
Deterministic, non-adaptive behavior
No automated response or enforcement paths
No remote command execution
This design is intentional and non-configurable.
5. Evidence & Data Responsibility
7MANGOOSE records telemetry and evidence as observed
We do not alter, interpret, or validate the legal significance of collected data
You retain full responsibility for:
Data retention
Evidence handling
Compliance use
Chain-of-custody procedures
6. No Security Guarantee
7MANGOOSE provides visibility, not protection.
We make no guarantee that:
Threats will be prevented
Attacks will be stopped
Systems will remain secure
7MANGOOSE is a truth and observation engine, not a defensive enforcement tool.
7. No Professional Advice
Information provided by 7MANGOOSE does not constitute:
Legal advice
Compliance certification
Regulatory approval
Incident response direction
Consult qualified professionals for those services.
8. Intellectual Property
All software, documentation, branding, and content related to 7MANGOOSE are protected by intellectual property laws.
You may not:
Resell or redistribute without authorization
Remove copyright or attribution notices
Claim ownership of the platform itself
9. Disclaimer of Warranties
The Services are provided “AS IS” and “AS AVAILABLE.”
We disclaim all warranties, including but not limited to:
Merchantability
Fitness for a particular purpose
Accuracy or completeness of observations
10. Limitation of Liability
To the maximum extent permitted by law:
7MANGOOSE and its operators shall not be liable for indirect, incidental, or consequential damages
Total liability shall not exceed the amount paid (if any) for use of the Services
11. Termination
We may suspend or terminate access if these Terms are violated. You may stop using the Services at any time.
Termination does not remove your responsibility for lawful use prior to termination.
12. Changes to These Terms
We may update these Terms periodically. Continued use of the Services after changes constitutes acceptance of the updated Terms.
13. Governing Law
These Terms are governed by the laws of the applicable jurisdiction where 7MANGOOSE is operated, without regard to conflict-of-law principles.
14. Contact
For questions about these Terms:
7MANGOOSE
Email: jesse@mangoose.com
Website: https://.7mangoose.com
